Memento Crypto
Your cryptographic protection is mortal. The calendar doesn’t lie.
There’s an ancient practice called memento mori. Latin for “remember that you will die.”
Not morbid. Clarifying.
The Stoics kept skulls on their desks. Medieval monks inscribed it on walls. Modern versions show up as life calendars—grids of boxes representing every week of an 80-year lifespan. Each filled box is a week spent. The remaining empty boxes are what you have left.
The insight isn’t that death is coming. Everyone knows that. The insight is that *seeing* it changes behavior now.
Finite time, made visible, creates urgency that abstract knowledge never does.
I want to apply that same thinking to something else that’s coming, that everyone in security knows about, and that almost no one is acting on with appropriate urgency.
Q-Day.
The wrong way to think about Q-Day
Q-Day is typically framed as a ticking bomb. A doomsday clock. The moment quantum computers become powerful enough to break RSA and elliptic curve cryptography, and everything falls apart.
That framing is understandable. It’s also counterproductive.
Apocalypse framing creates paralysis, not action. After two decades of quantum hype, another warning about cryptographic collapse just bounces off. Security leaders have heard it before. They’ll hear it again. The date keeps moving. The sky hasn’t fallen yet.
Meanwhile, the actual risk accumulates quietly, every single week, in a way the doomsday frame completely obscures.
What the calendar actually shows
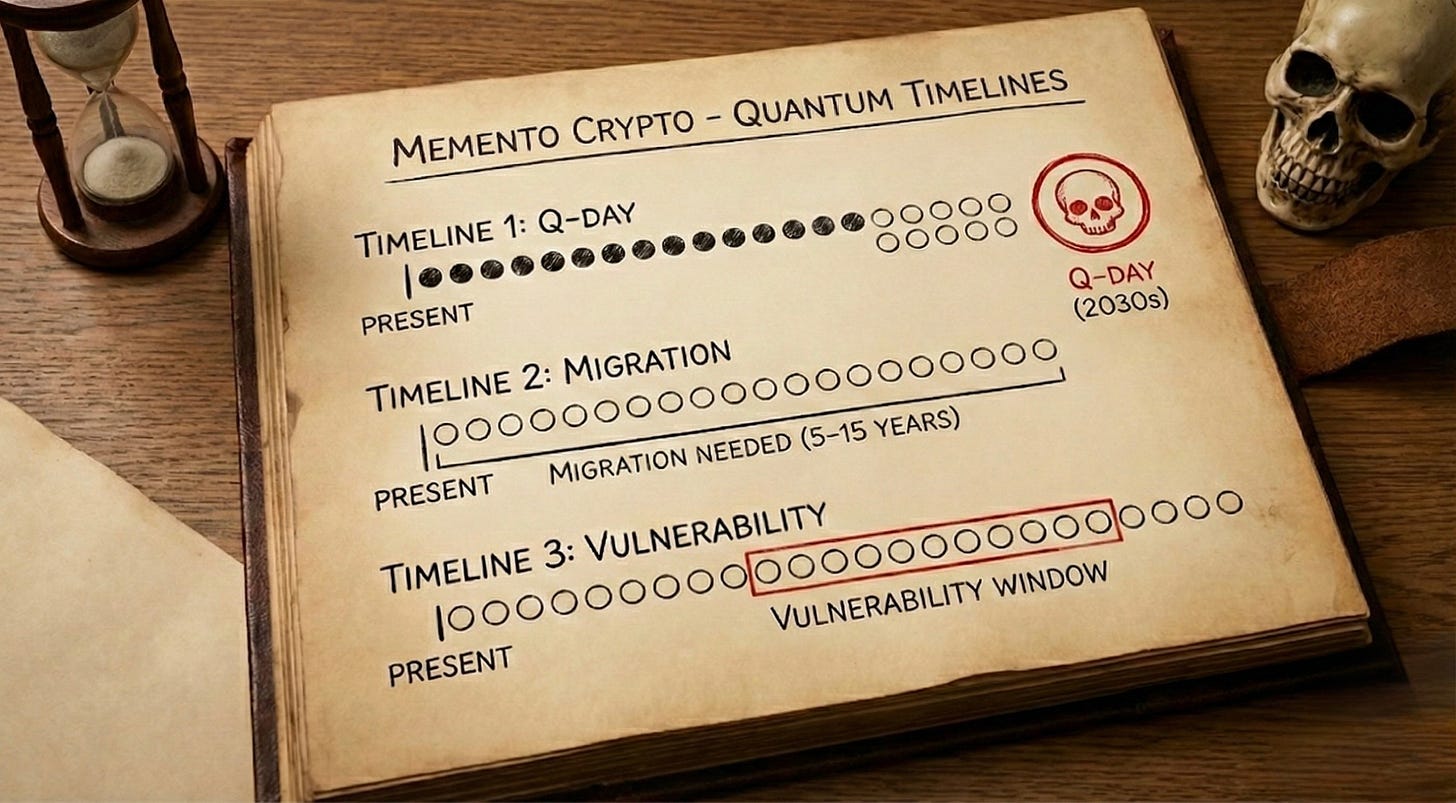
Forget Q-Day as a single moment. Think instead about three overlapping timelines.
Timeline 1: Weeks until Q-Day
Based on current evidence—IBM’s fault-tolerant roadmaps, Google’s below-threshold error correction with Willow, Microsoft’s topological qubit work, the algorithmic improvements that reduced estimated qubit requirements from 20 million to around 1 million—most experts place cryptographically relevant quantum computers somewhere in the early 2030s.
Call it 260 to 360 weeks from now. Five to seven years.
That’s not a prediction. It’s a range that reflects genuine uncertainty. It could be sooner. It could be later. But the median expert estimate has been drifting earlier, not later.
Timeline 2: Weeks your organization needs to migrate
This is where the math gets uncomfortable.
A 2025 academic study published in MDPI analyzed realistic migration timelines across enterprise sizes. Their findings:
- Small enterprises: 5 to 7 years
- Medium enterprises: 8 to 12 years
- Large enterprises: 12 to 15+ years
These numbers include discovery, inventory, cryptographic asset mapping, vendor coordination, hybrid deployment, testing, compliance, and rollout. They account for the reality that cryptography touches everything—every application, every protocol, every device, every partner integration.
Gartner’s analysis aligns: full enterprise migration takes most of a decade.
NIST’s own transition guidance (IR 8547) sets 2030 as the deprecation target for quantum-vulnerable algorithms and 2035 for full disallowance.
Timeline 3: The overlap gap
Now put them together.
If Q-Day arrives in 2031, and your migration takes 12 years, you needed to start in 2019.
If Q-Day arrives in 2031, and your migration takes 7 years, you needed to start in 2024.
If you haven’t started yet, draw the timelines yourself. See where they cross.
The gap between them—the period where Q-Day has arrived but your migration isn’t complete—is your vulnerability window. The weeks where your data is exposed, your signatures can be forged, your infrastructure is compromised.
Every week you delay starting makes that window wider.
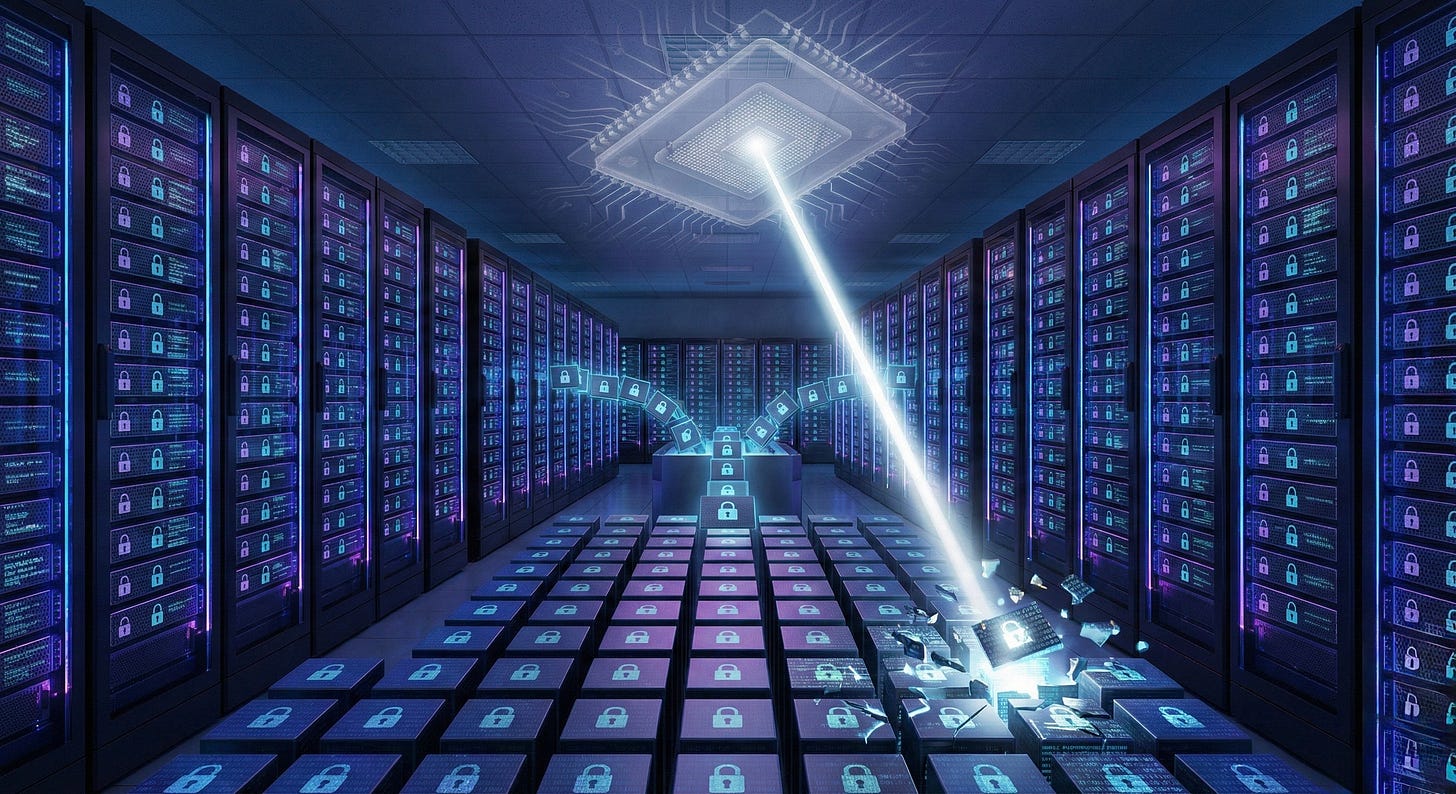
The harvest calendar
There’s another calendar that matters even more.
Adversaries don’t need quantum computers today. They only need storage and patience. The strategy is called harvest now, decrypt later. Capture encrypted traffic today. Wait for quantum capability. Decrypt everything retroactively.
This means the risk window isn’t waiting for Q-Day to open.
It’s already open.
Consider data created this week with a 15-year confidentiality requirement. Healthcare records. Identity credentials. Firmware signing keys. Infrastructure secrets. Strategic communications.
If that data is captured today and Q-Day arrives in 2030, an adversary gains access to information that was supposed to remain protected until 2040. They get ten years of unauthorized access to secrets that were never meant to be exposed.
Every week that passes is a week of data added to the harvest pile. Data that cannot be un-captured. Data whose exposure is locked in the moment Q-Day arrives.
A memento mori calendar for this would look something like:
```
2025: ░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░
2026: ░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░
2027: ░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░
2028: ░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░
2029: ░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░░
2030: ████████████████████████████████████████████████████ ← Q-Day
2031: ████████████████████████████████████████████████████
2032: ████████████████████████████████████████████████████
```
Every unfilled box before Q-Day represents a week of data captured under classical encryption. The moment Q-Day arrives, every one of those boxes turns solid. Exposed. Retroactively compromised.
You cannot un-harvest what has already been collected.
The quantum progress that’s making this real
This isn’t theoretical concern anymore. The past year saw technical milestones that moved expert timelines forward.
Google’s Willow chip (December 2024) demonstrated below-threshold error correction for the first time. As qubits scaled from 3×3 to 5×5 to 7×7 arrays, error rates decreased by half at each step. This is the fundamental unlock that fault-tolerant quantum computing requires. Qubit coherence times improved from 20 microseconds to 68 microseconds. The chip performed a benchmark computation in under five minutes that would take classical supercomputers 10 septillion years.
IBM’s roadmap now targets 200 logical qubits running 100 million quantum gates by 2029 (Starling), scaling to 2,000 logical qubits and 1 billion gates by 2033 (Blue Jay). Their qLDPC error correction codes reduce physical qubit overhead by 90% compared to previous approaches. Their RelayBP decoder achieves real-time error correction in under 480 nanoseconds.
Microsoft’s Majorana 1 (February 2025) introduced the first topological qubit processor, using an entirely new class of materials called topoconductors. The approach promises inherent error resistance at the hardware level. The scientific community is still evaluating these claims, but DARPA selected Microsoft as one of two companies to advance to the final phase of their quantum benchmarking program.
Amazon’s Ocelot (February 2025) demonstrated the first scalable cat qubit chip, claiming 90% reduction in error correction overhead compared to conventional approaches. Cat qubits intrinsically suppress certain error types, potentially shortening the path to fault tolerance.
Craig Gidney’s algorithmic work (2025) showed that factoring RSA-2048 could require approximately 1 million physical qubits—down from the 20 million estimated in 2019. That’s a 20× reduction in hardware requirements, achieved purely through better algorithms.
Multiple approaches. Multiple breakthroughs. Converging timelines.
The classical correction that made quantum honest
Not all the important quantum news has come from quantum labs.
In 2019, Ewin Tang presented work at STOC—one of the most respected computer science conferences—that forced the entire field to recalibrate its claims. Tang showed that several widely cited quantum machine learning algorithms, including quantum recommendation systems, lost their claimed exponential speedups when compared against properly optimized classical algorithms under equivalent data-access assumptions.
The quantum algorithms weren’t wrong. The classical baselines they’d been compared against were too weak.
Tang’s “dequantization” work demonstrated that classical randomized and sampling-based techniques had been systematically underestimated. When you gave classical algorithms the same data-access model quantum algorithms assumed, the gap often disappeared or shrank dramatically.
This matters for two reasons.
First, it forced rigor. Quantum advantage claims now face sharper scrutiny. You can’t just beat a naive classical baseline and declare victory. You have to beat the best known classical approach, and you have to specify your assumptions precisely. The field became more honest.
Second—and this is the part that often gets missed—some quantum algorithms survived the scrutiny. Tang’s own work showed that quantum approaches to topological data analysis resisted dequantization. There are problems where quantum speedups appear genuine. The difference is that now we know which ones, and why.
Tang received the 2025 Maryam Mirzakhani New Frontiers Prize for this work. It didn’t slow quantum computing down. It cleaned quantum computing up.
For the Q-Day timeline, this means the threat is real but bounded. Shor’s algorithm for factoring integers and breaking elliptic curves has not been dequantized. The cryptographic risk remains. But the hype around general quantum supremacy has been tempered by proof that classical computers are more capable than many assumed.
The calendar still runs. But we read it with clearer eyes.
What the other side looks like
The good news is that the destination exists.
NIST finalized post-quantum cryptographic standards in August 2024:
- FIPS 203 (ML-KEM): Module-lattice-based key encapsulation for secure communications
- FIPS 204 (ML-DSA): Module-lattice-based digital signatures for authentication
- FIPS 205 (SLH-DSA): Stateless hash-based signatures for long-term use cases
These aren’t proposals. They’re federal standards, available now.
Cloudflare reports that by the end of 2024, 50% of requests to their network used hybrid post-quantum key exchange (X25519MLKEM768). By March 2025, 38% of all HTTPS traffic on the internet was using post-quantum algorithms. Chrome, Edge, and Firefox have all deployed support.
Certificate authorities including DigiCert now support ML-DSA and SLH-DSA for private certificates, with ML-KEM support in development. Full post-quantum trust chains can be tested today.
The bridge across exists. The question is whether you start crossing before the ground behind you disappears.
Memento Crypto
The Stoics didn’t keep skulls on their desks because they wanted to be depressed. They did it because they understood something about human psychology.
We discount the future. We treat distant threats as abstract. We assume we’ll have time later. We’re wrong.
The skull made mortality concrete. Present. Undeniable. And that changed behavior.
Memento Crypto is the same practice, applied to cryptographic mortality.
Your protection is finite. The calendar is running. Every week that passes is a week of data exposed to future harvest, a week of migration runway consumed, a week closer to a vulnerability window you may not be able to close.
This isn’t doom. This is math.
The organizations that see the calendar clearly will act now—inventorying cryptographic assets, building crypto-agility, deploying hybrid protections, testing post-quantum trust chains. They’ll treat migration as infrastructure modernization, not emergency response. They’ll finish before the window closes.
The organizations that don’t see it clearly will discover, sometime in the early 2030s, that they needed more time than they had.
The calendar doesn’t lie.
The only question is whether you’re looking at it.
If you’re ready to start: DigiCert’s post-quantum solutions support ML-DSA and SLH-DSA certificates today, with ML-KEM support coming. The TrustCore SDK includes all three NIST-standardized algorithms. Testing is available now—before the calendar runs out.